The answer to Assume Breach
Most breaches aren’t detected for months. Tracebit detects them in seconds. Deploy canaries across your environment that trigger high-fidelity alerts when attackers move laterally, escalate privileges or access credentials.
Modern security programs depend on deception as a core control, and Tracebit delivers it at the highest level.

Chief Information Security Officer
Canary-based detection is a critical layer in Docker’s defense-in-depth strategy. Tracebit makes deploying and managing deception at scale practical.
.webp)
Chief Information Security Officer, Docker
The Tracebit platform delivered on their promise of low friction and low noise. We were able to quickly and confidently roll out Tracebit!

Head of Security, IT & Compliance
Tracebit’s platform enables high fidelity alerts, is quick to deploy, easy to maintain and secure by design. Their solution delivers actual value and is getting better by the day.

Head of Security
We deployed something like a few hundred canaries within our environment, and it took… a few minutes. It’s been pretty seamless for us.
Lead SOC Analyst
As part of our comprehensive, multi-layered security model, Tracebit provides the vital, dynamic detection layer.

VP Security and CISO

The question isn’t if you’ll be breached. It’s how fast you’ll know. The average attacker spends 11 days inside an environment before anyone notices. Traditional detection hunts for patterns in billions of events. Tracebit instead deploys canaries across your environment, producing a precise and actionable alert the moment an attacker touches one.
Your environment fights back.
Most security investments make your team better at defending. Deception makes attackers worse at attacking. Your SIEM, your EDR, your firewall all respond to what attackers do. Deception changes what attackers are willing to do.
Analyze

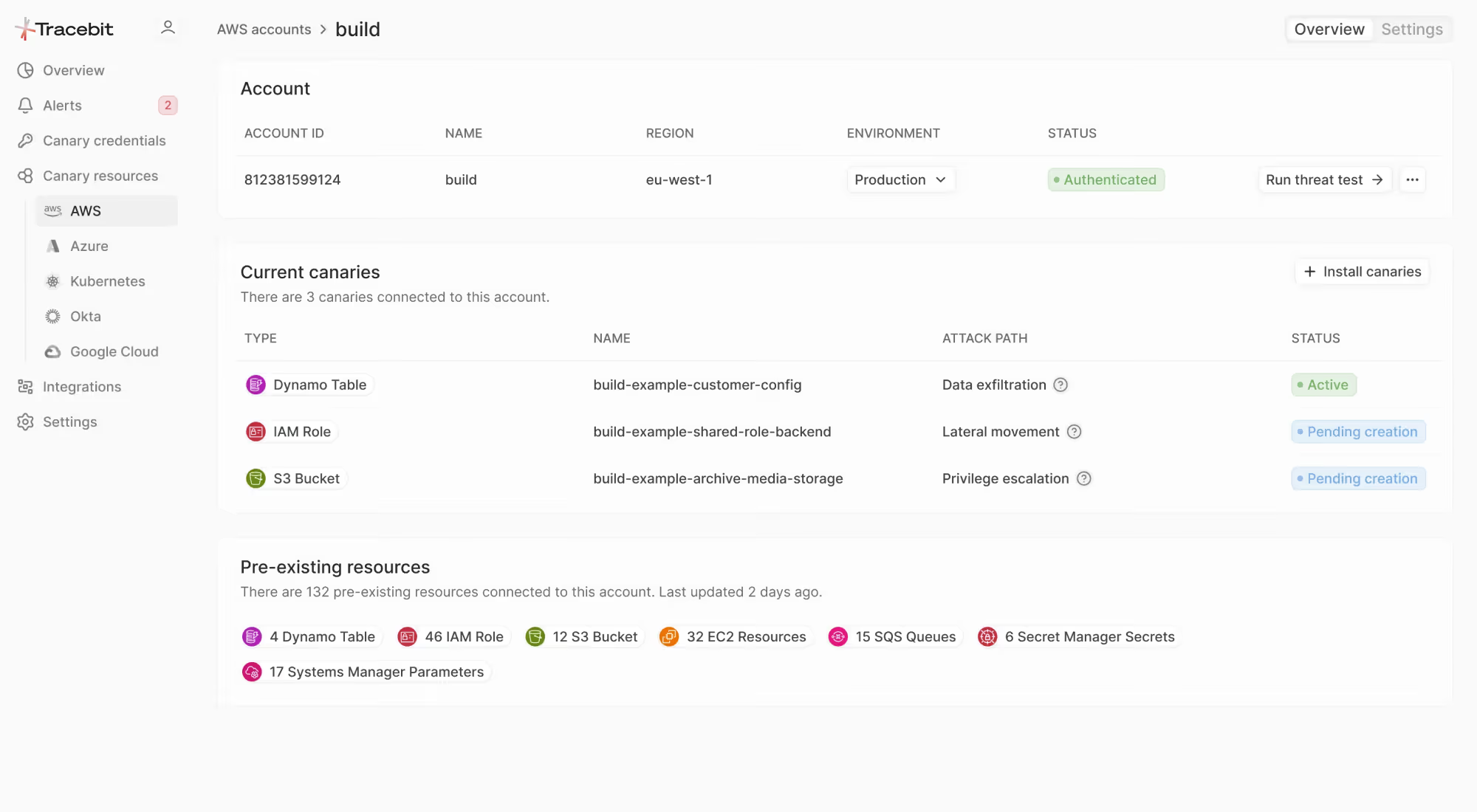
Tracebit intelligently understands your environment
Deploy

LLM driven suggestions create a hostile environment for attackers
Detect

Canary detections rapidly pinpoint threat actor behavior
Detection belongs at the start of your security program.
High fidelity detections that integrate into your stack. Get notified instantly with high signal, low noise, actionable alerts.

Modern security teams are using Tracebit’s Deception Technology to enable Assume Breach

Protect your environment with Tracebit
Book a demo today.
FAQs.
Answered.
How does Tracebit detect attackers?
Tracebit uses deception to detect attacker behavior after initial access. It deploys realistic canary resources and credentials across your environment, inside your perimeter.
When an attacker enumerates, accesses, or attempts lateral movement, they touch a canary, and Tracebit generates an immediate high-confidence alert.Unlike traditional tools, Tracebit doesn't rely on known signatures or suspicious patterns. It detects the behavior attackers can’t avoid.
What do you deploy — and is it safe?
Tracebit deploys realistic decoy resources (like buckets, secrets, credentials and identities) that are safe by design. They contain no real data and don’t impact production systems. Canaries are designed to look valuable to attackers while remaining isolated and non-disruptive. If they’re accessed, it’s a strong signal of compromise — without introducing risk to your environment.
How long does it take to set up?
Most teams deploy Tracebit in minutes. Tracebit integrates with your existing infrastructure using a lightweight connection (often via Terraform for cloud environments). There are no agents to install and no network changes required. Once connected, Tracebit deploys and manages canaries automatically as your environment evolves.
How is this different from SIEM, EDR, or CSPM?
SIEM, EDR, and CSPM tools are valuable — but they typically rely on logs, rules, known indicators, and policy evaluation. That often creates detection gaps, noise, and missed post-breach activity.
Tracebit is different: it creates high-confidence detection by placing realistic canaries where attackers naturally move. When those canaries are touched, it’s a clear signal — even for novel attacks — and it produces far fewer false positives. Tracebit complements your existing stack by adding a post-breach detection layer.














